this post was submitted on 01 Jul 2024
444 points (90.4% liked)
linuxmemes
21222 readers
65 users here now
Hint: :q!
Sister communities:
- LemmyMemes: Memes
- LemmyShitpost: Anything and everything goes.
- RISA: Star Trek memes and shitposts
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack members of the community for any reason.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
- These rules are somewhat loosened when the subject is a public figure. Still, do not attack their person or incite harrassment.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn. Even if you watch it on a Linux machine.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, and wants to interject for a moment. You can stop now.
Please report posts and comments that break these rules!
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
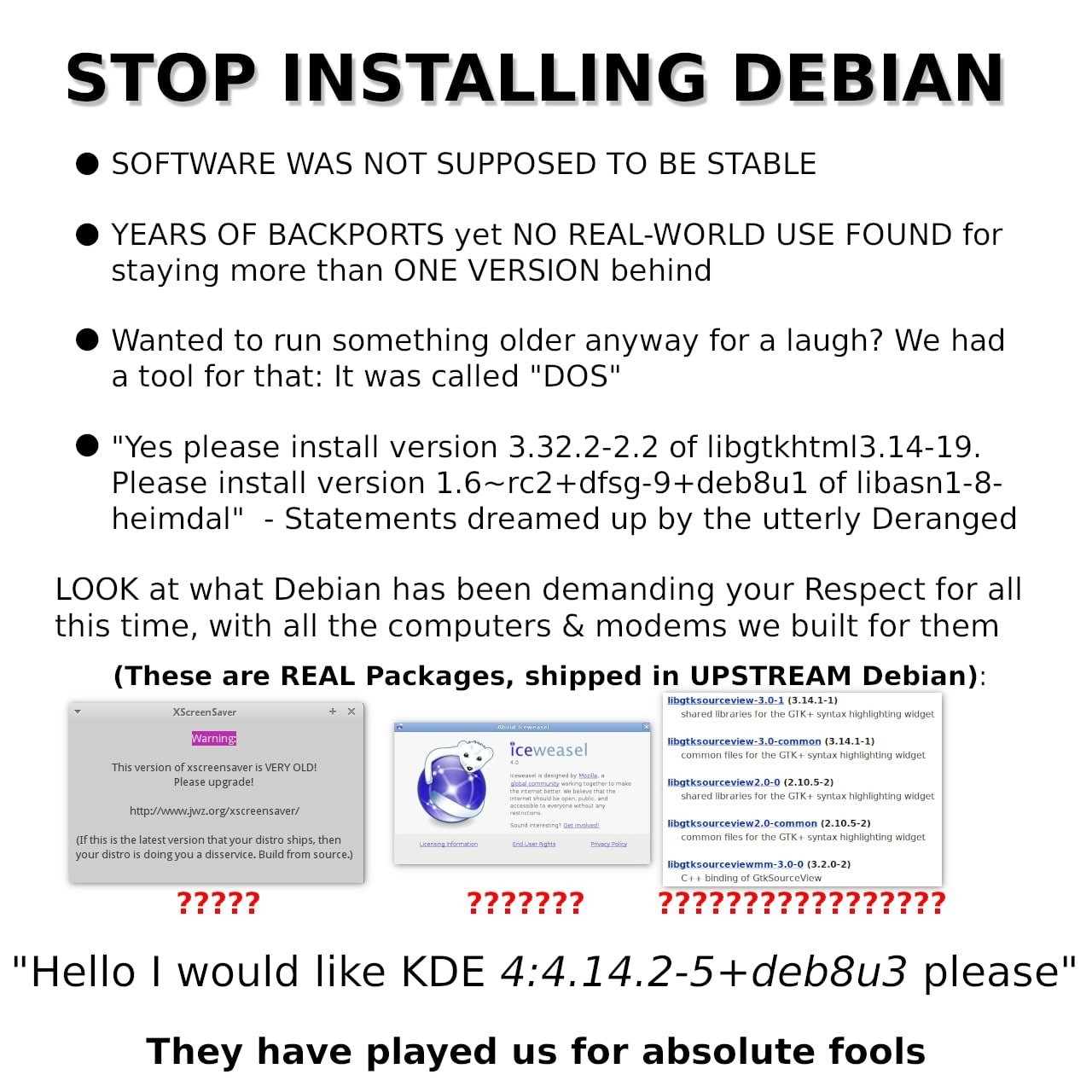
The ssh vulnerability didn’t affect Debian because the packages were too many versions behind
AFAIK, the xz vulnerability was designed for Debian based on its workaround fixing systemd service status detection. Even if it shipped to something like Arch, the malicious code wouldn’t load.
Security through Geriatricity
Except this isn't true at all.
https://security-tracker.debian.org/tracker/CVE-2024-6387
Regresshion impacted bookworm and trixie both. Buster was too old.
With the downside of me doing an apt update and seeing that openssh-server was on
1:9.2p1-2+deb12u3and I had no idea at a glance if this included the fix or not (qualys's page states version 8.5p1-9.8p1 were vulnerable).If you are running debian bookworm or trixie, you absolutely should update your openssh-server package.
Isn’t this meme format completely written in sarcasm?
We're on a meme page. There is little difference between sarcasm and being serious here. It doesn't matter whether OP is being fully sarcastic or fully serious, people in the comments may hold the same opinion seriously, sarcastically, or with a mixture of both. The format is irrelevant
The xz/ssh back door made it into Debian testing, So I felt I should wipe and reinstall.
Debian has had a rolling release for ages.