this post was submitted on 23 Apr 2024
1050 points (97.0% liked)
Memes
48297 readers
1669 users here now
Rules:
- Be civil and nice.
- Try not to excessively repost, as a rule of thumb, wait at least 2 months to do it if you have to.
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
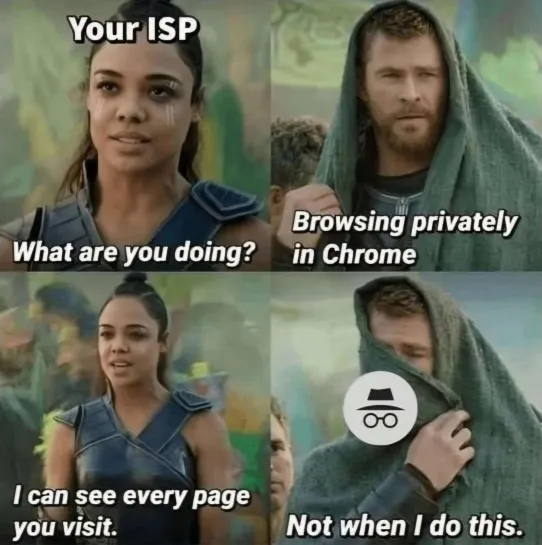
DoT also encrypts the request, so the ISP cannot spy on the Domain Name you have requested.
And thanks to Https the ISP only sees the IP address which cannot in every case be resolved to a unique Domain, especially large sites that are hosted on service providers like Cloudflare, amazon etc etc
But what's not encrypted by either is the Server Name Indicator or SNI, ie: the initial request to a webserver stating which host you're trying to reach at that IP, before establishing the TLS connection, contains the domain you'd requested via DoH/DoT, in plaintext.
encrypted SNI is a thing now.
True. Known as Encrypted Client Hello now, as part of TLS1.3.
It seems many more browsers support it than last I'd looked. I'm curious to see how much of the general web has adopted support for it onnthe server side. I'll have to look into that more, and see what it'll take to setup for self-hosting.
That is correct. HSTS helps to some degree but the very first request is still unprotected.
https://www.cloudflare.com/learning/dns/dns-over-tls/
If I understand it correctly DoH (which I use with NextDNS) should prevent ISP from snooping.
It will prevent the ISP from snooping on, or tampering with, the DNS request. However when you go to use the IP you've retrieved via DoH/DoT; your first request establishing a TLS connection to that IP will contain an unencrypted SNI which states the domain you are trying to use. This can be snooped on by your ISP.